Hostwinds Tutorials
Search results for:
Table of Contents
Background Process Killer Overview In WHM
Tags: WHM
Within WHM, there comes the ability to automatically kill processes that are related to IRC Bots and Servers. Usually, this is more of a concern if there is shell access allowed for the cPanel user.
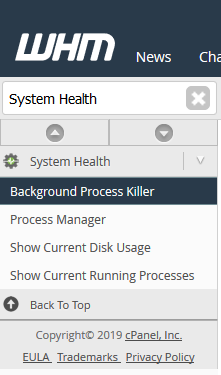
Where To Find The Background Process Killer
Step One: Log into your WHM Administrative Dashboard.
Step Two: From WHM, in the upper left, search for 'System Health. ' In the available options will be Background Process Killer. Click on this to be brought to the Background Process Killer management page.
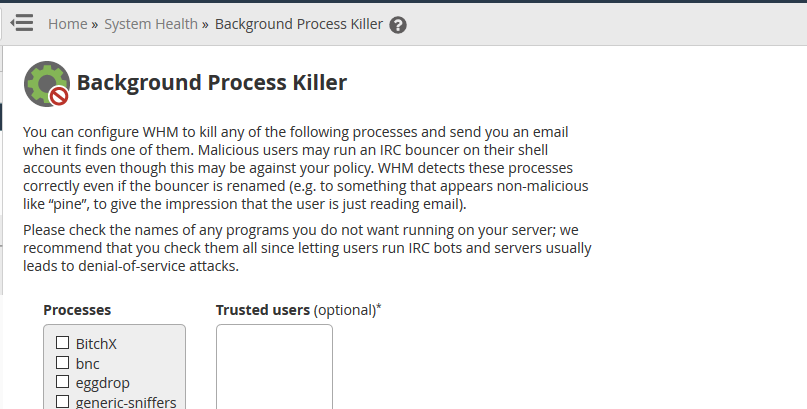
The Background Process Killer page may look like below, where you can select check boxes next to the disabled processes and add Trusted users if needed.
Background Processes That Can Be Killed
With the list of Processes displayed on the Background Process Killer page, you may not be familiar with all of them. Normally it would be recommended to disable all of them by clicking on the checkmark next to each one.
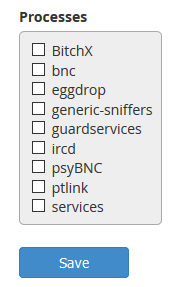
- BitchX – a popular Free IRC Client
- BNC – This is an IRC bouncer. A Bouncer can be used to hide the source connected to a server and may be used in Denial Of Service Attacks
- eggdrop – eggdrop is an IRC bot that can execute a set of commands on an IRC server. In some cases, it may be used to create a botnet for Denial Of Service Attacks.
- Generic-sniffers – Sniffers are typically used to collect and investigate packets of information that are transferred between computers.
- Guard services – This is another example of an IRC bot that can execute a set of commands on an IRC server.
- ircd – This is the daemon that is used to host an IRC Server.
- psyBNC – Similar to BNC, this would also be an IRC Network Bouncer
- services – Like guard services and egg drop, services is another IRC bot.
Once you have selected the processes you don't want to be running, click on the blue Save button to save the changes.
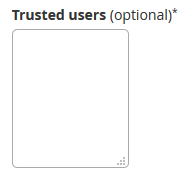
Adding Trusted Users
From the Background Process Killer page, you can also add in Trusted users that will be allowed to run the processes that you have disabled without having the processes killed.
To add Trusted Users, you can enter them into the text box underneath Trusted Users from the Background Process Killer page. Make sure the usernames are spelled correctly and that there is only one username per line. Once you are done, click the blue Save button to save the changes.
Written by Hostwinds Team / January 28, 2019
